Cyber Security at Sea
Exploring cyber security at sea, how protected are vessels at sea? What should be done and what standards and frameworks could be applied.
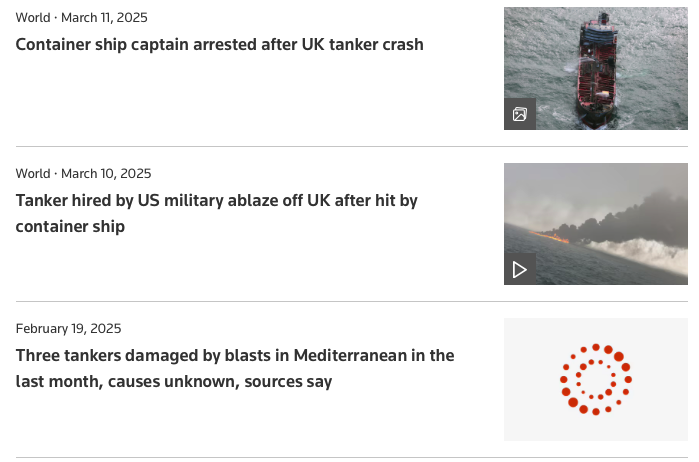
A few years ago I attended an Information Security Europe exhibition in London. I was awestruck with a number of presentations that day, one of which is currently at the forefront of my mind. With the collision just outside of the Humber estuary of a tanker full of jet fuel for the US military – everyone is currently asking was this some sort of nefarious act? How do we apply cyber security at sea?
In short, it’s unlikely – but it is plausible.
A cyber attack would be just one means of achieving the same goal – disruption of the supply chain and sending a message about how fragility of global shipping. The reality is that it would be easier and more achievable by leveraging a crew member on board who could just as easily do the same thing – make two very large boats hit each other.
The presentation
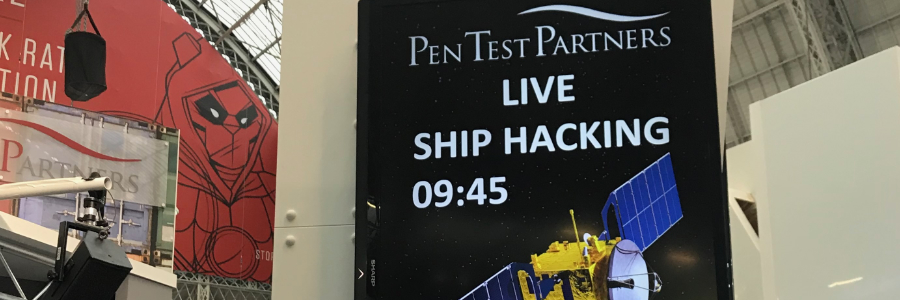
So let’s skip back to 2018 and a company called ‘Pen Test Partners’ that gave a ‘real life’ presentation of cyber security at sea. By hacking ship systems and making boats think that they are somewhere different to their actual position you can cause disruption and even endanger life. This wasn’t some national state ‘gps’ jamming, but changing ‘Operational Technology’ (OT) systems to ignore and replace the data that they had with something more nefarious. We all knew the ‘internet of things’ was bad back then, but to give it is correct ‘OT’ name – things are still just as bad.
This set a seed in my mind. Cyber security at sea was a ‘thing’. Could it be another ‘niche’ service that Unshakeable Salt could provide ?
The good news is that standards such as Industrial Control Systems (ISA/ IEC 62443) tackle the generic Operational Technology aspect. The NIS2 directive can provide the framework and assurance over the application, ensuring that all the necessary processes are in place.
So with NIS2 and ISA/ IEC 62443 experience gained (and listed on my CV), the other element I was missing was the context of maritime operations and the threat exposure to vessels at sea. Whilst I don’t list that I have a skippers license on my CV (I do – but only for vessels under 20m in length – not a million tonne MV), but I do have some understanding of the threat exposure.
Threat Modelling
What additional threats does operation of a ship at sea have? What systems could a threat actor exploit to disrupt and block global supply chains? How would an attack present itself and how could a watch leader on the bridge know about it?
The reality is that cyber security at sea is very complex. This is compounded by very old devices that have an extremely long life ahead of them being connected to modern control systems. Those control systems are normally air-gapped from networks, but it only takes a slight misconfiguration and they could be open to the world – but in most cases, just being open to networks on the ship itself is enough.
Six years have passed and the world has indeed moved on since that original presentation. Shipping is listed as one of the 13 sectors within the definition of Critical National Infrastructure. We have both the National Cyber Security Center (NCSC) and the National Protective Security Authority (NPSA) setting standards for protection in the UK.
Critical National Infrastructure (CNI) are those facilities, systems, sites, information, people, networks and processes, necessary for a country to function and upon which daily life depends. It also includes some functions, sites and organisations which are not critical to the maintenance of essential services, but which need protection due to the potential danger to the public.
An Approach
Treating a ship as just another industrial control system and securing using ISA/ IEC 62443 is a fantastic start. Each vessel having a roadmap to mature and improve would prevent a cyber attack from disrupting a vessels operation. For the cost of operation and prevention of disruption, it would be a good cost effective way to reduce risk and ensure integrity and availability of the vessel.
Then there is the ‘however….’ issue. Cyber security at sea would have to be enforced – with each geographic region potentially having different requirements. Looking at the Portuguese flagged MV Solong being operated by a Russian captain and Filipino crew in British waters, the combination of nations complicates matters. Neither the NCSC nor the NPSA would have authority over non-British vessels operating within UK waters. Looking at the ships register and port audits, one of the vessels lists a plethora of safety issues such as missing fire fighting equipment and faulty doors. When a vessel is being operated with those missing, what are the chances of it actually applying cyber security controls ?
Even if we could decide on international standards for cyber security at sea, the likelihood of them being applied and enforced is improbable.
Lets face it
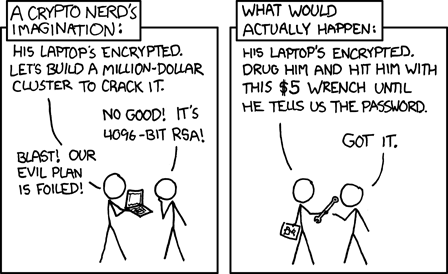
The above XKCD comic strip comes to mind here. There are 1001 quicker, cheaper and better ways to stop a ship from getting from A to B than launching a cyber attack. Even if a cyber attack was easy because of the lack of standards, lack of enforcement and lack of willingness to be secure – it would still be easier and more effective to apply pressure to a member of crew to perform the nefarious action without making a single keystroke.
It would still be nice though if we could apply cyber security at sea.
View Comments
Everything as Code
In today’s fast-paced digital world, businesses demand agility, reliability, and...